When people worry about protecting themselves from hackers, it’s usually their computer that they’re concerned about. No one concerns themselves with their printers, or their webcams, or their home security systems because nobody can hack them… right?
As technology becomes more focused on connectivity, cloud computing, and being wireless, it inevitably becomes more intertwined with the internet. How is your iPhone able to control that RC helicopter? They’re connected through the internet. How is your HD camera able to send pictures directly to your computer? They’re connected through the internet.
More and more of our technology is being impetuously intertwined with the internet in order to achieve the abilities that modern consumers demand. Nobody is worried about connecting these devices to the internet because nobody thinks that hackers will target HD cameras or RC helicopters, and that’s the biggest issue.
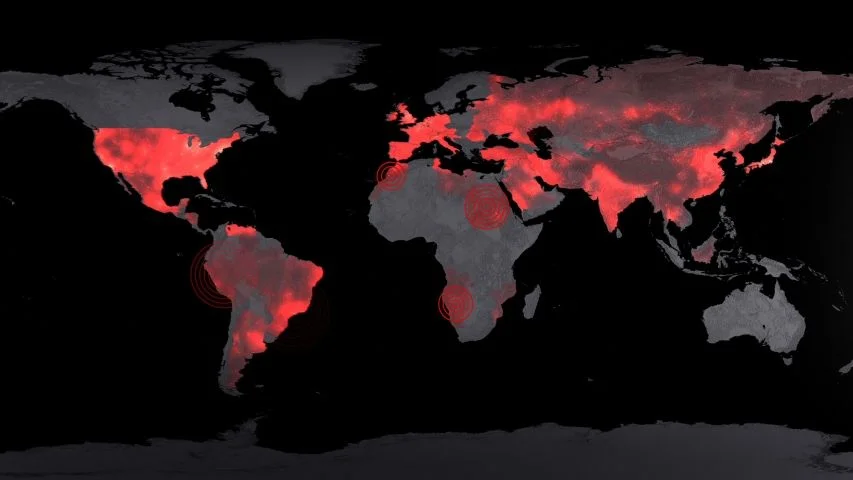
Since nobody anticipates these devices being hacked, there aren't any security measures being put into place to protect them. Fortunately for us, it’s incredibly difficult for hackers to locate these devices. Unfortunately for us, there’s a search engine dedicated to doing exactly that.
The Shodan Search Engine is like a creepier version of Google. Instead of navigating millions of websites, Shodan navigates millions of devices and these devices aren't limited to just the previously mentions webcams, printers, or HD cameras. When I said that more and more of our technology is being intertwined with the internet, I meant ALL of our technology. From traffic lights to nuclear power plants, even our infrastructure is connected to the internet and Shodan has access to it all.
While Shodan brings to attention to potential dangers of “connected” technology, it has yet to be used to exploit those dangers. In fact, Shodan has been used almost exclusively for good since its creation. Most cyber criminals are looking to steal money and intellectual property, not set off nuclear reactors. These people usually already have access to the tools they’d need to accomplish these goals and as such, don’t need Shodan. Several security professionals have even begun to seek out vulnerable devices on Shodan and alert the users before hackers with malicious intent can find them.
About the Author
Jesseb Shiloh is new to blogging. He enjoys things that most don't and dismisses society as an unfortunate distraction.