Iran's nuclear efforts have been more than a bit of a threat, and with that, US and Israel joined forces to create their own weaponry, Stuxnet. Stuxnet is a computer worm that was discovered in June 2010 to slow Iran's nuclear efforts.
After copies of the worm leaked, it was available on the internet in late 2010, early 2011. Therefore, intelligence agencies in the US and Israel sought out new targets that could further slow Iran's progress down. The worm consists of a layered attack against 3 different systems: Siemens PCS 7, WINCC, and Step7. That is, until Tiffany Rad, a hacker altered the code. Demonstrating how she could use the code to control prison doors, without alerting the guards.
After the code was hacked into, Stuxnet was turned off on June 24, 2012. With the shutting down of Stuxnet, the framework may have become the blueprint for the next big cyber weapon. Cyber warfare is not over, in fact, DUQU has striking similarities to Stuxnet and according to researchers, 50% of the source code and 99% of the software rules for DUQU are the same as Stuxnet. To avoid suspicion from network administrators, DUQU camouflages its own data behind normal web traffic. Cyber warfare is going on around us and we probably don't even know it, so, what's next?
Check out this infographic presented by Veracode to learn more.
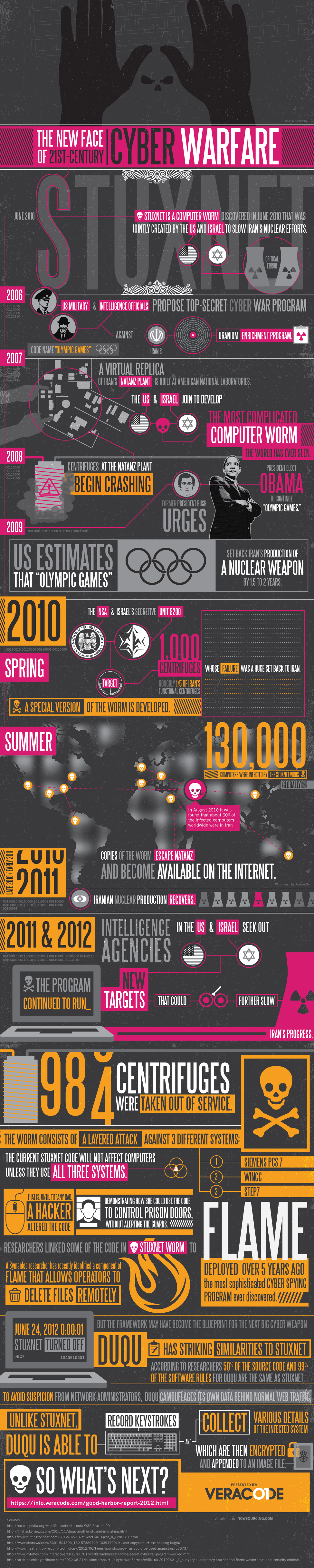
Infographic by Veracode Application Security